Google’s Threat Analysis Group (TAG) works to counter targeted and government-backed hacking against Google and the people who use our products. Following our November update, today we’re sharing the latest insights to fight phishing, and for security teams, providing more details about our work identifying attacks against zero-day vulnerabilities.
Protecting you from phishing
We have a long-standing policy to send you a warning if we detect that your account is a target of government-backed phishing or malware attempts. In 2019, we sent almost 40,000 warnings, a nearly 25 percent drop from 2018. One reason for this decline is that our new protections are working—attackers' efforts have been slowed down and they’re more deliberate in their attempts, meaning attempts are happening less frequently as attackers adapt.
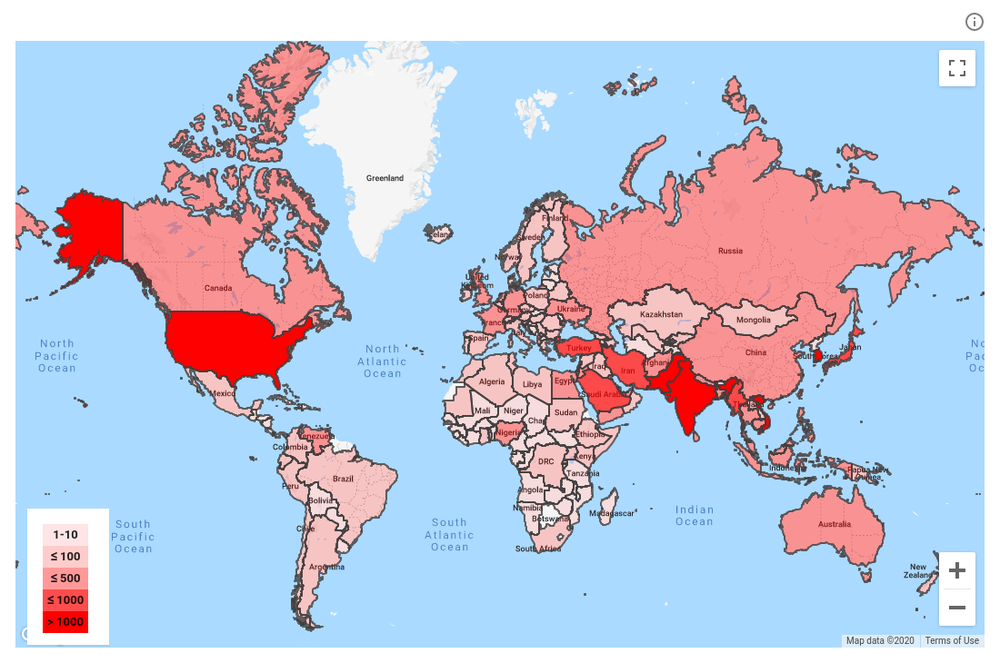
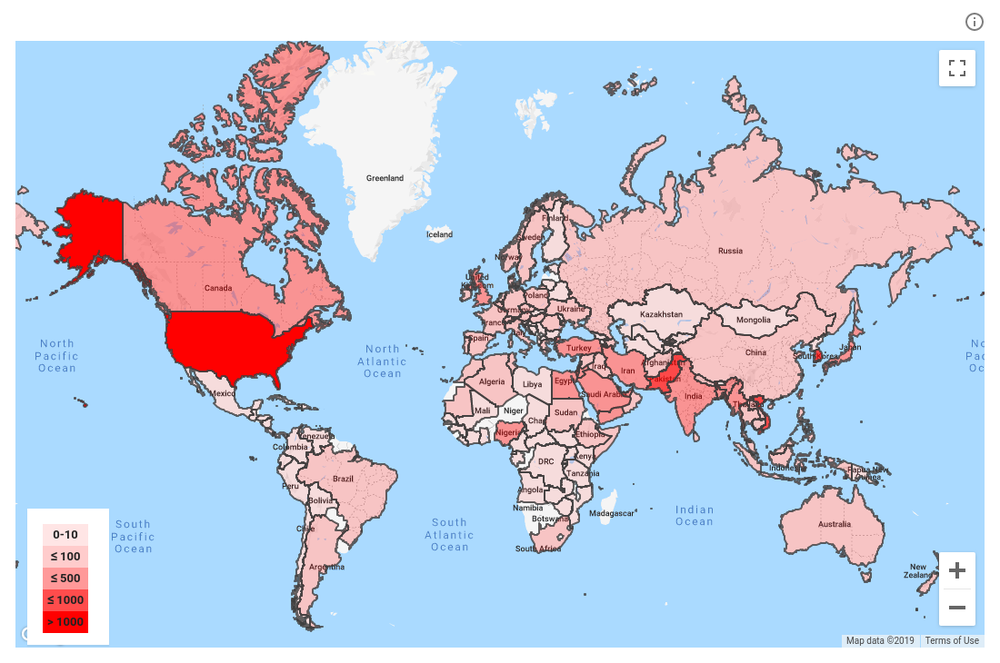
Distribution of the targets of government-backed phishing in 2019.
We’ve detected a few emerging trends in recent months.
Impersonating news outlets and journalists is on the rise
Upon reviewing phishing attempts since the beginning of this year, we’ve seen a rising number of attackers, including those from Iran and North Korea, impersonating news outlets or journalists. For example, attackers impersonate a journalist to seed false stories with other reporters to spread disinformation. In other cases, attackers will send several benign emails to build a rapport with a journalist or foreign policy expert before sending a malicious attachment in a follow up email. Government-backed attackers regularly target foreign policy experts for their research, access to the organizations they work with, and connection to fellow researchers or policymakers for subsequent attacks.
Heavily targeted sectors are (mostly) not surprising
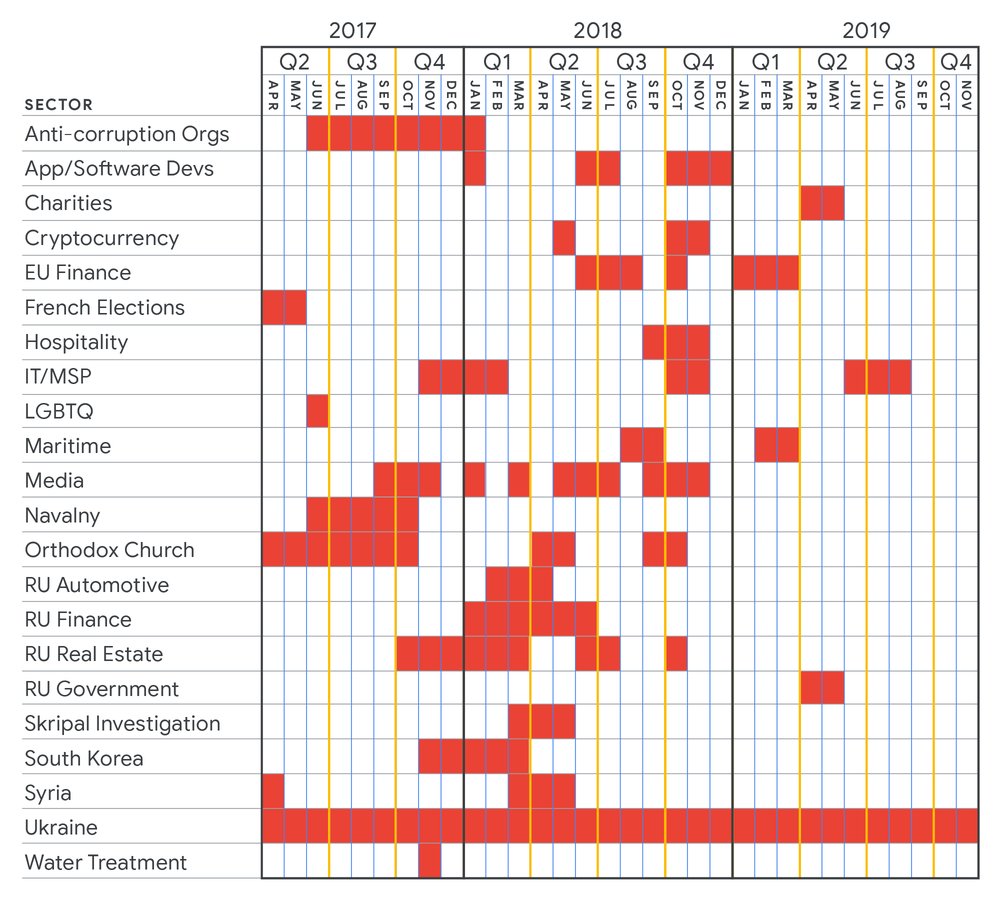
Government-backed attackers continue to consistently target geopolitical rivals, government officials, journalists, dissidents and activists. The chart below details the Russian threat actor group SANDWORM’s targeting efforts (by sector) over the last three years.
Government-backed attackers repeatedly go after their targets
In 2019, one in five accounts that received a warning was targeted multiple times by attackers. If at first the attacker does not succeed, they’ll try again using a different lure, different account, or trying to compromise an associate of their target.
We’ve yet to see people successfully phished if they participate in Google’s Advanced Protection Program (APP), even if they are repeatedly targeted. APP provides the strongest protections available against phishing and account hijacking and is specifically designed for the highest-risk accounts.
Finding attacks that leverage zero-day vulnerabilities
Zero-day vulnerabilities are unknown software flaws. Until they’re identified and fixed, they can be exploited by attackers. TAG actively hunts for these types of attacks because they are particularly dangerous and have a high rate of success, although they account for a small number of the overall total. When we find an attack that takes advantage of a zero-day vulnerability, we report the vulnerability to the vendor and give them seven days to patch or produce an advisory or we release an advisory ourselves.
We work across all platforms, and in 2019 TAG discovered zero-day vulnerabilities affecting Android, Chrome, iOS, Internet Explorer and Windows. Most recently, TAG was acknowledged in January 2020 for our contribution in identifying CVE-2020-0674, a remote code execution vulnerability in Internet Explorer.
Last year, TAG discovered that a single threat actor was capitalizing on five zero-day vulnerabilities. Finding this many zero-day exploits from the same actor in a relatively short time frame is rare. The exploits were delivered via compromised legitimate websites (e.g. watering hole attacks), links to malicious websites, and email attachments in limited spear phishing campaigns. The majority of targets we observed were from North Korea or individuals who worked on North Korea-related issues.
For security teams interested in learning more, here are additional details about the exploits and our work in 2019:
The vulnerabilities underlying these exploits included:
Internet Explorer - CVE-2018-8653
Internet Explorer - CVE-2019-0676
Chrome - CVE-2019-5786
Windows Kernel - CVE-2019-0808
Internet Explorer - CVE-2019-1367
Internet Explorer - CVE-2019-1429
The following technical details are associated with the exploits and can be used for teams interested in conducting further research on these attacks:
CVE-2018-8653, CVE-2019-1367 and CVE-2020-0674 are vulnerabilities inside jscript.dll, therefore all exploits enabled IE8 rendering and used JScript.Compact as JS engine.
In most Internet Explorer exploits, attackers abused the Enumerator object in order to gain remote code execution.
To escape from the Internet Explorer EPM sandbox, exploits used a technique consisting of replaying the same vulnerability inside svchost by abusing Web Proxy Auto-Discovery (WPad) Service. Attackers abused this technique with CVE-2020-0674 on Firefox to escape the sandbox after exploiting CVE-2019-17026.
CVE-2019-0676 is a variant of CVE-2017-0022, CVE-2016-3298, CVE-2016-0162 and CVE-2016-3351 where the vulnerability resided inside the handling of “res://” URI scheme. Exploiting CVE-2019-0676 enabled attackers to reveal presence or non-presence of files on the victim’s computer; this information was later used to decide whether or not a second stage exploit should be delivered.
The attack vector for CVE-2019-1367 was rather atypical as the exploit was delivered from an Office document abusing the online video embedding feature to load an external URL conducting the exploitation.
Our Threat Analyst Group will continue to identify bad actors and share relevant information with others in the industry. Our goal is to bring awareness to these issues to protect you and fight bad actors to prevent future attacks. In a future update, we’ll provide details on attackers using lures related to COVID-19 and expected behavior we’re observing (all within the normal range of attacker activity).